
Como o Barracuda Managed XDR está a manter as organizações seguras em meio à atividade cibernética ligada ao conflito no Médio Oriente
Monitorização ativa de ameaças em evolução, caça proativa de ameaças em ambientes de clientes, IoCs continuamente atualizados, e mais
Principais conclusões
- O SOC global do Barracuda Managed XDR registou um aumento de 10 vezes no tráfego de rede malicioso do Irão para os Estados Unidos a 25 de fevereiro, pouco antes do início do conflito.
- A equipa SOC está a operar num estado de alerta elevado, protegendo os clientes de riscos que evoluem rapidamente.
- Os clientes também são aconselhados a reforçar as medidas de segurança essenciais para gerir o risco.
Pouco antes do início do conflito no Médio Oriente, o Centro de Operações de Segurança (SOC) global da Barracuda Managed XDR observou um aumento notável na atividade cibernética, com um aumento de 10 vezes no tráfego malicioso do Irão para os Estados Unidos. Este pico reflete a intensa e amplamente relatada atividade cibernética entre o Irão, os seus adversários, os seus aliados e outros países. As ameaças continuam a evoluir.
Para manter os clientes protegidos, a equipa SOC está atualmente a operar num estado de alerta elevado de prontidão e a realizar ativamente a monitorização de ameaças e a busca proativa de ameaças em ambientes de clientes.
Monitorização e medidas práticas
O SOC continua a monitorizar o panorama de ameaças e a implementar medidas de proteção adicionais à medida que a situação evolui.
O SOC está a integrar ativamente na sua plataforma de inteligência de ameaças todas as ameaças maliciosas verificadas que se originam ou estão ligadas a atores cibernéticos iranianos — como domínios, endereços IP e URLs. A plataforma de inteligência de ameaças já contém cerca de 14 mil milhões de indicadores de compromisso, incluindo aqueles relacionados com o atual conflito no Médio Oriente.
Os ambientes dos clientes são analisados assim que uma nova ameaça é identificada.
As regras de segurança e detecções para a solução de Endpoint Detection and Response (EDR) do Barracuda Managed XDR, fornecida através do SentinelOne, são continuamente atualizadas com as informações mais recentes.
Os clientes que utilizam a funcionalidade SentinelOne devem considerar ativar as regras da Platform Detection Library, caso ainda não o tenham feito, para alargar ainda mais a cobertura.
As seguintes regras de EDR são mostradas para proteger contra operações cibernéticas iranianas atualmente conhecidas:
Categoria de ameaça |
Nome da regra |
Descrição |
MuddyWater |
Possível DLL MuddyWater Drop Consistente com Carregamento Lateral de Driver de Áudio |
Detecta uma biblioteca de ligação dinâmica (DLL) a ser escrita de uma forma utilizada pelo grupo de ciberespionagem MuddyWater |
Extração de credenciais |
Criação de Tarefa Suspeita para Colheita de Credenciais |
Detecta um evento de criação de tarefa que executa ferramentas utilizadas para roubo de credenciais |
|
Ferramenta de Exploração de Rede Baseada em Python |
Deteta ferramentas de hacking baseadas em Python usadas para movimento lateral e atividades de pós-exploração |
|
Ferramentas Potenciais de Dumping LSASS |
Detecta a presença de ferramentas comuns usadas para extrair credenciais no Serviço de Subsistema de Autoridade de Segurança Local (LSASS) |
|
Extracção de Credenciais via Cópia Sombra |
Detecta o roubo de credenciais através de cópias sombra |
|
Colheita Interativa de NTDS via VSS |
Detecta tentativas iniciadas pelo utilizador para recolher NTDS.dit através do Volume Shadow Copy Service (VSS) |
|
Despejo de Credenciais de Domínio em Cache |
Detecta a listagem de credenciais em cache usando cmdkey.exe |
Tunneling e acesso remoto |
Domínio Ngrok Contactado |
Deteta DNS para domínios ngrok |
|
Estabelecimento de Túnel Persistente Cloudflare Detetado |
Detecta o estabelecimento persistente de túnel Cloudflare |
|
Processo Anómalo a Iniciar Tráfego de Túnel do Cloudflare |
Detecta processos invulgares a estabelecer um túnel Cloudflare |
Coleção & exfiltração |
Script de Keylogging via PowerShell |
Detecta PowerShell utilizando funções que podem ser usadas para registo de teclas |
|
Informações do Navegador Chromium roubadas via Depuração Remota |
Detecta a depuração remota em navegadores Chromium a ser utilizada para colheita de credenciais |
|
Tentativa de Acesso a Dados de Credenciais e Cookies do Navegador |
Deteta tentativas de acesso a credenciais e cookies |
Abuso de PowerShell/script |
Execução de Script PowerShell via IPv4 Inteiro Baseado em Tempo |
Detecta execução de PowerShell que executa scripts remotos enquanto utiliza IPv4 de inteiros baseados no tempo |
|
Utilização suspeita de .NET Reflection via PowerShell |
Detecta reflexão .NET a partir de scripts PowerShell |
|
Linha de Comando de Download de Lançamento de PowerShell Codificado |
Detecta comandos PowerShell codificados que iniciam um download |
Evasão de defesa, impacto, descoberta |
Potencial DLL Sideloading no Diretório PerfLogs |
Detecta o carregamento lateral de DLL no diretório PerfLogs |
|
Tentativa de Limpeza de Dados de Disco via Utilitário Dd |
Deteta a utilização da utilidade de definição do conjunto de dados (dd) para limpar um disco |
|
Manipulação da Configuração de Arranque através do BCDEdit |
Deteta a modificação dos dados de configuração de arranque (BCD) para maximizar a perturbação através do BCDEdit |
|
Criação de Ficheiro de Reconhecimento do BloodHound Active Directory |
Detecta a execução de BloodHound e ferramentas alternativas |
Medidas de segurança recomendadas para todas as empresas
Juntamente com a proteção cibernética resiliente, profunda e 24/7 fornecida por uma solução de segurança como o Barracuda Managed XDR, existem passos práticos que as organizações podem tomar para aumentar a sua resiliência cibernética durante períodos de risco elevado. Estes incluem:
Segurança de rede
- Implemente o bloqueio a nível de país no firewall para regiões onde a sua organização não realiza negócios
- Desative implementações voltadas para o público do Remote Desktop Protocol (RDP), aplique autenticação multifator para todo o acesso remoto e monitore logs para logins falhados e incomuns. Bloqueie pessoas após três a cinco tentativas falhadas e considere substituir o RDP por infraestrutura de desktop virtual (VDI) em vez de RDP direto.
- Verifique se existem portas de acesso remoto não utilizadas e desative-as se não estiverem em uso.
- Implemente a segmentação de rede para limitar o movimento lateral
- Utilize estações de trabalho de acesso privilegiado (PAWs) para tarefas administrativas
Configurações do firewall
- Revise todas as regras de firewall de entrada e saída
- Remova todas as regras que estão definidas como "permitir qualquer"
- Documente e justifique todas as regras de acesso externo
- Preste especial atenção às regras que permitem o acesso a partir de intervalos de IP estrangeiros
Políticas de palavras-passe
- Impor palavras-passe longas (14 caracteres)
- Exigir complexidade: maiúsculas, minúsculas, números e caracteres especiais
- Impeça a reutilização de senhas e considere impor atualizações de senhas a cada 60 a 90 dias
Outras medidas essenciais
- Priorizar atualizações de software
- Verifique as aplicações instaladas em todos os dispositivos corporativos e remova as aplicações não autorizadas ou desnecessárias.
- Preste especial atenção às ferramentas de acesso remoto, como o TeamViewer e o AnyDesk
- Procure por ferramentas legítimas que possam ser abusadas – incluindo PSExec e PowerShell ISE
- Certifique-se de que os seus sistemas de backup estão isolados e testados, e mantenha backups offline de dados críticos.
- Revise e atualize o seu plano de resposta a incidentes
Para mais assistência, entre em contacto com a equipa Barracuda Managed XDR para ver como podem ajudar.
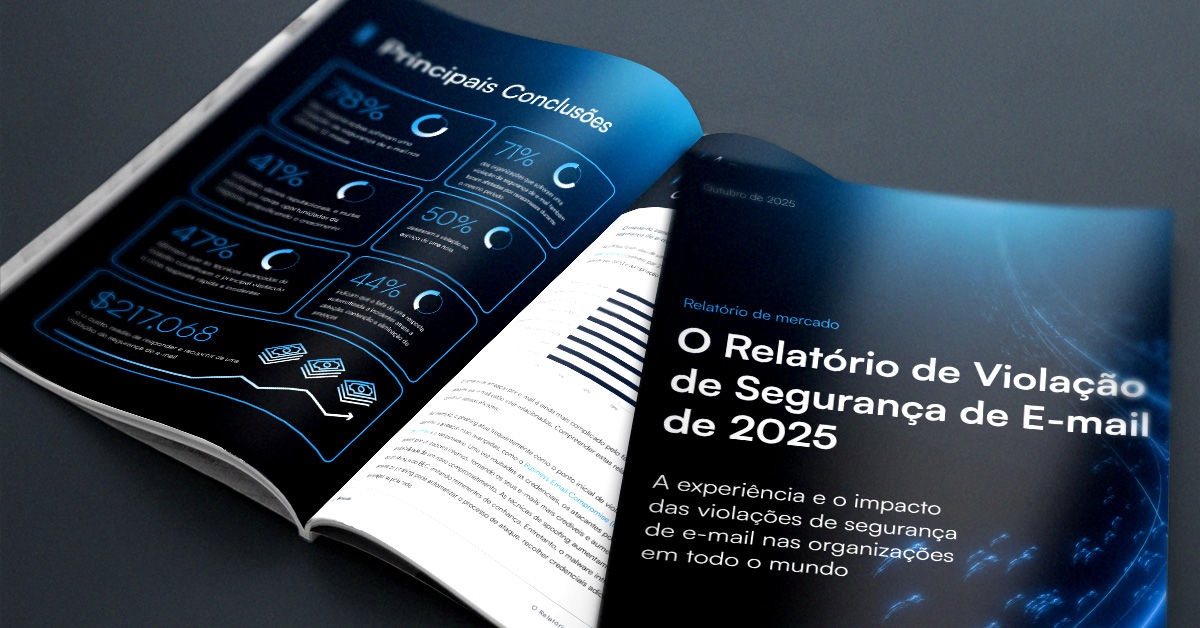
O Relatório de Invasão de Segurança de E-mail de 2025
Principais conclusões sobre a experiência e o impacto das violações de segurança de e-mail em organizações em todo o mundo
Subscreva o Blogue Barracuda.
Inscreva-se para receber destaques sobre ameaças, comentários do setor e muito mais.

Relatório de Insights do Cliente MSP 2025
Uma visão global sobre o que as organizações precisam e desejam dos seus provedores de serviços geridos de cibersegurança





